Meraki MRxx with external RADIUS authentication (recommended)
SOCIFI is proud to be Cisco Meraki Technology Partner
This article applies to the following models:
MR12, MR16, MR18, MR26, MR34, MR62, MR66, MR72
Are you missing some options in the Meraki Dashboard? Continue here.
Tested versions:
| Model | Type | Firmware version | Description |
|---|---|---|---|
| MR12, MR18, MR32 | AP | AP |
Intro:
If you want to use some SOCIFI features (bandwidth management, PayThru, roaming) you'll have to set external RADIUS on your Meraki controller. SOCIFI recommends to use configuration with the external RADIUS as the first choice. The following steps can slightly differ for each Meraki type, but the logic of settings is the same. Settings for Meraki Z1 and Meraki MR12 follows.
Note: The configuration without RADIUS authentication can be found here: Meraki without external RADIUS authentication.
Common Issues & resolutions:
Are you missing some options in the Meraki Dashboard?
1. Log into Meraki Dashboard
2. RADIUS server setting
Select Wireless > Access control. Pick the SSID you want to work with and on the Network access in the Splash page section please check Sign-on with and pick "my RADIUS server". In the RADIUS for splash page section please add the Primary RADIUS server first and then Secondary as follows:
We recommend to use this set of RADIUS servers:
| Host | < name > (e.g. rad-1-euw-1.socifi.com) |
|---|---|
| Port | 1812 |
| Secret | socifi |
Note: the port 1813 for accounting is created automatically
Pages related to RADIUS issues
Running Radius test on Cisco Meraki
In the Failover Policy section select "Deny Access" and in the Network access control section select "Disabled: do not check clients for antivirus software"
3. Walled garden ranges setting
Select Walled garden > set Walled garden is enabled
Enter following Walled garden ranges:
If you are a customer with the White Label solution, please add your custom domain (for example *.mycustomdomain.com) to the Walled Garden list.
*.socifi.com *.facebook.com *.akamaihd.net *.akamai.net *.edgecastcdn.net twitter.com *.twitter.com *.twimg.com *.fastly.net *.li-cdn.net *.cloudfront.net facebook.com *.fbcdn.net *.instagram.com *.cdninstagram.com instagram.com *.linkedin.com *.licdn.com linkedin.com
facebook.com and twitter.com (Yes, twice. Once with and once without the asterisk)
Pages related to Walled Garden issues
Set the following values:
| Captive portal strength | Block all access until sign-on is complete |
|---|---|
| Walled garden | Walled garden is enabled |
| Walled garden ranges | < copy from the list above> |
| Simultaneous logins | Allow simultaneous device per user |
| Controller disconection behavior | Default for your settings |
4. Splash page Setup
Go to Wireless > Splash page and select Custom splash URL then enter: http://connect.socifi.com
5. Get the MAC address you'll need later for the SOCIFI dashboard administration
Go to Wireless > Access points and select wished AP. The MAC address is Configuration details (as pictured)
6. Add a new hotspot to SOCIFI Dashboard
Dashboard WiFi vendor setting
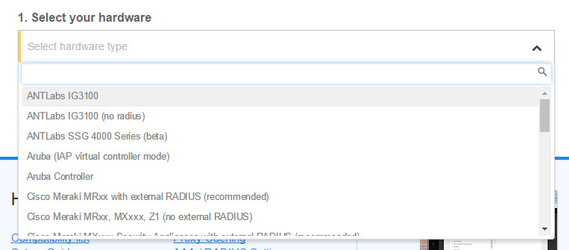
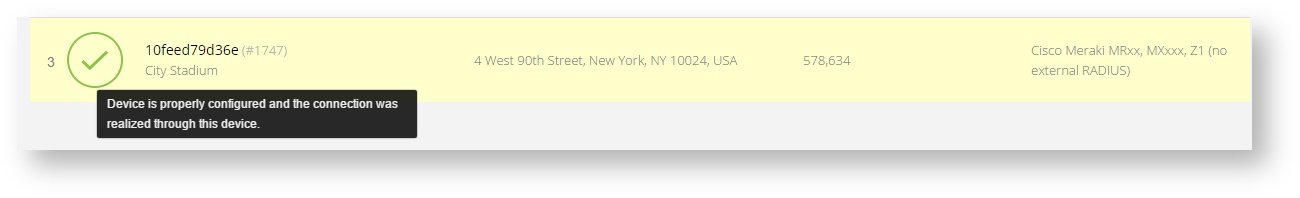
For the Dashboard administration, you'll need to know the MAC address of the Meraki device. As the Wifi vendor it the Hardware tab please Cisco Meraki (radius)
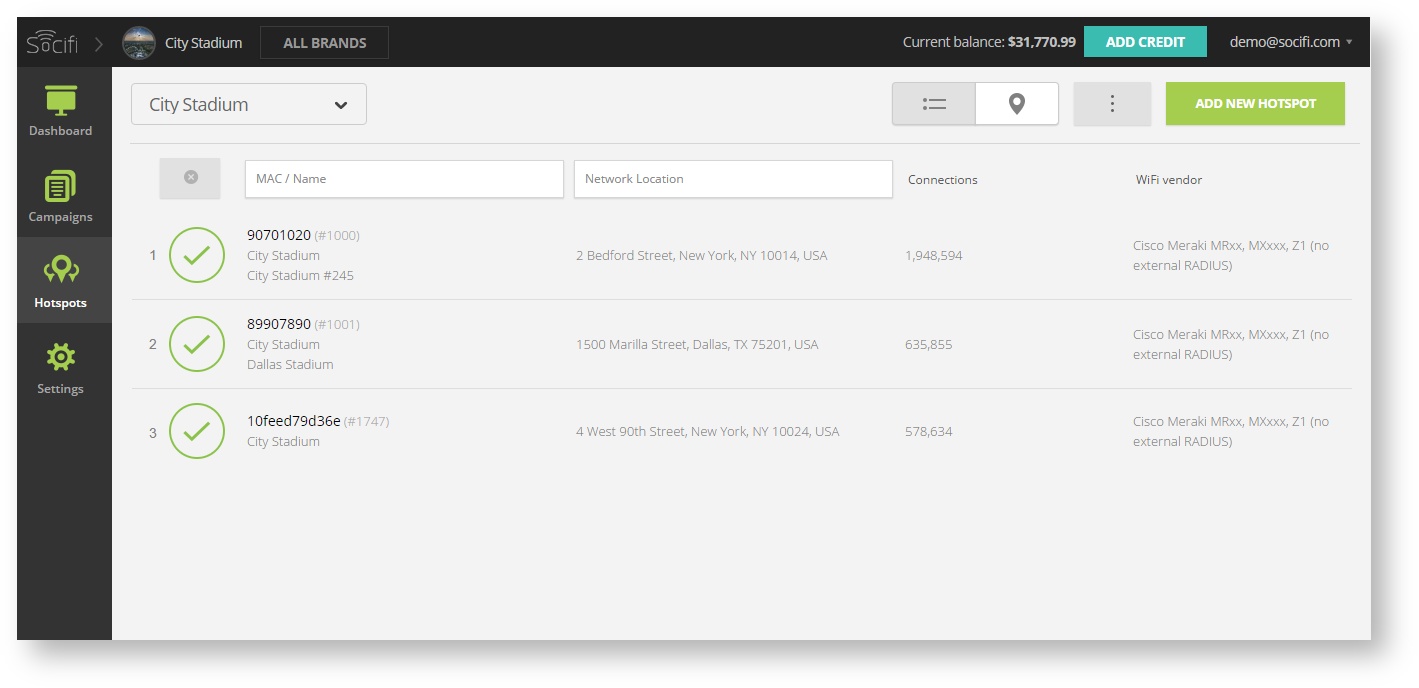
Step 1: Login to SOCIFI Dashboard
Step 2: Click on the "Hotspots" tab on the left sidebar
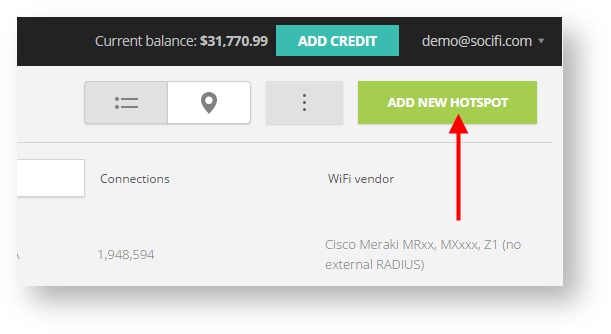
Step 3: Click on the “Add a new hotspot” button located on the top right corner on the screen (pictured below)
Note: A pop-up window will appear (below)
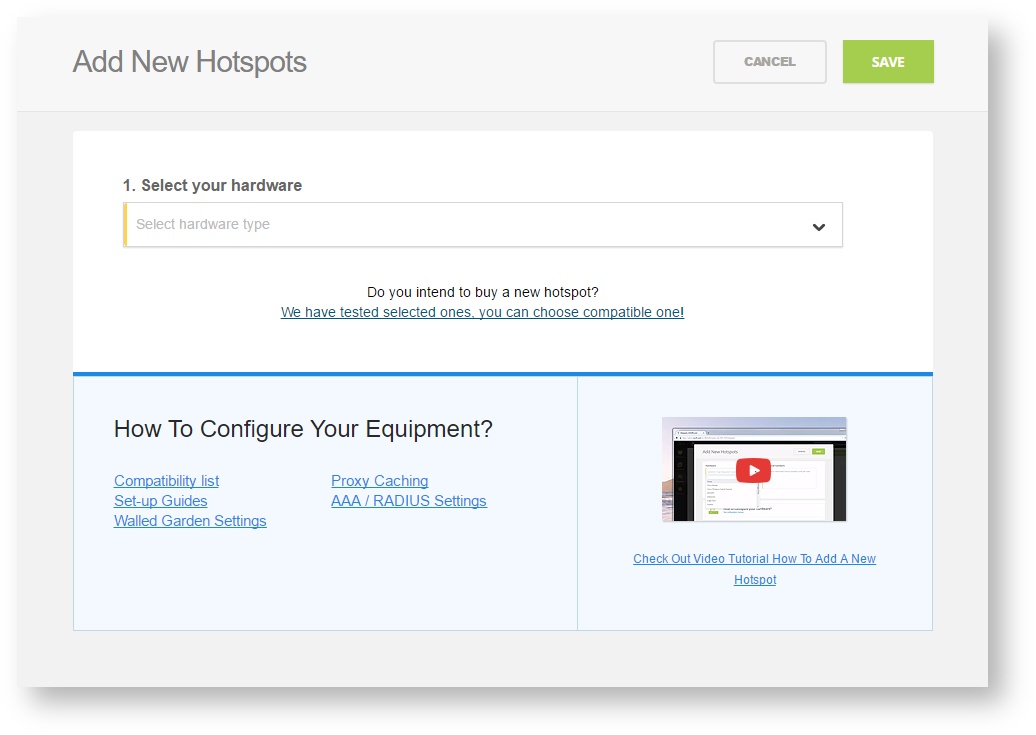
Step 4: Select the Wi-Fi hardware manufacturer from the drop down menu
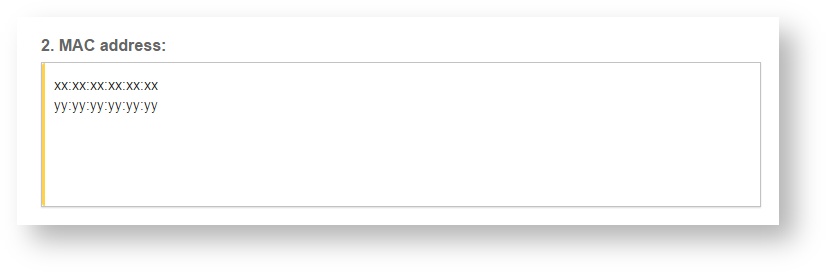
Step 5: Enter the serial number or MAC address (depending on the specific equipment manual) of your equipment. You can add multiple hotspots at once.
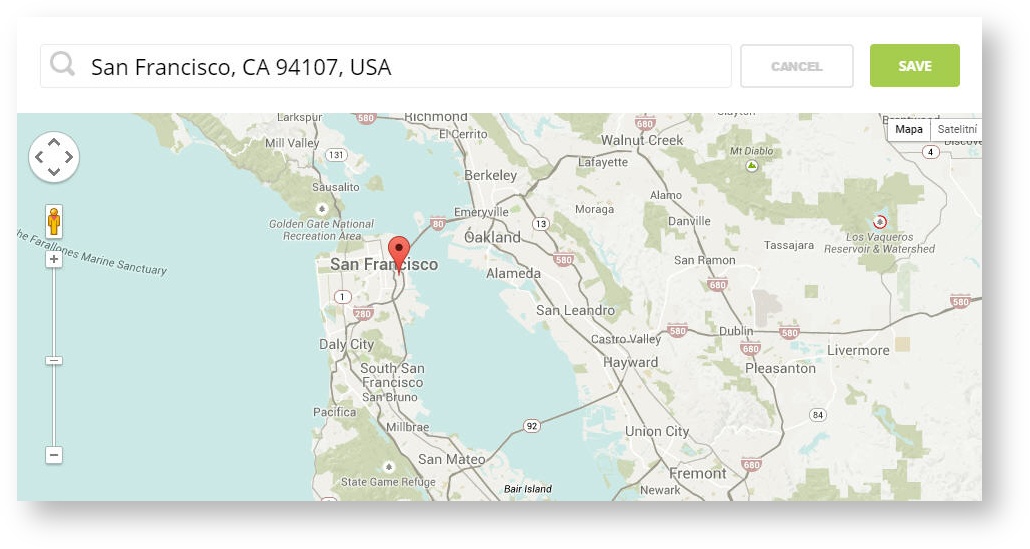
Step 6: Set your Network location (this step is essential for correct ad targeting)
Step 7: In the pop-up window type your location or just move the marker on the map and click on the save button to confirm the selection. This address is used for ad GEO targeting.
Step 7: Click Save
Note: Newly added hotspot are marked as (Hotspot pending). After the first user connects to the hotspot via SOCIFI, the status will automatically change and appear as (Active) within an hour. Get your first connections to test if it works properly.